recent posts
about
Author: Rutger Blom
-
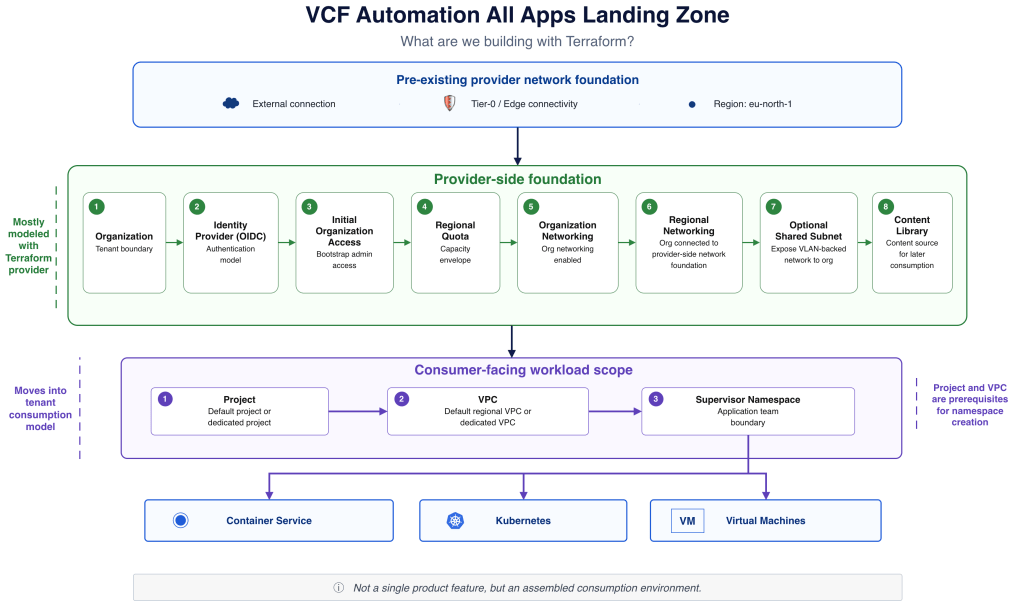
Terraform can describe parts of a VCF Automation 9.1 All Apps landing zone, but not the full model end to end. In this post I walk through the first layers of the landing zone foundation, including organization creation, identity provider configuration, quota, networking, content library and namespace consumption, while also calling out where the current…
-
I wanted to test organization-level OIDC authentication in VCF Automation 9.1 using Keycloak from my Provider Box setup. It worked in the end, but a few small details around group claims and claims mapping were easy to miss.
-
Self-service without guardrails is just delegated infrastructure access with a nicer interface. In this post I look at guardrails in the VCF Automation 9.1 All Apps model, and how organizations, quotas, namespaces, networking, policies, and extensibility work together to make private cloud consumption safer and more repeatable.
-
In my previous article, I reflected on what I would design differently if I were building an NSX platform today. That piece focused on architectural choices — fewer abstractions, clearer boundaries, stronger defaults. But design decisions are only part of the story. What ultimately matters is who carries responsibility for how the platform behaves over…
-
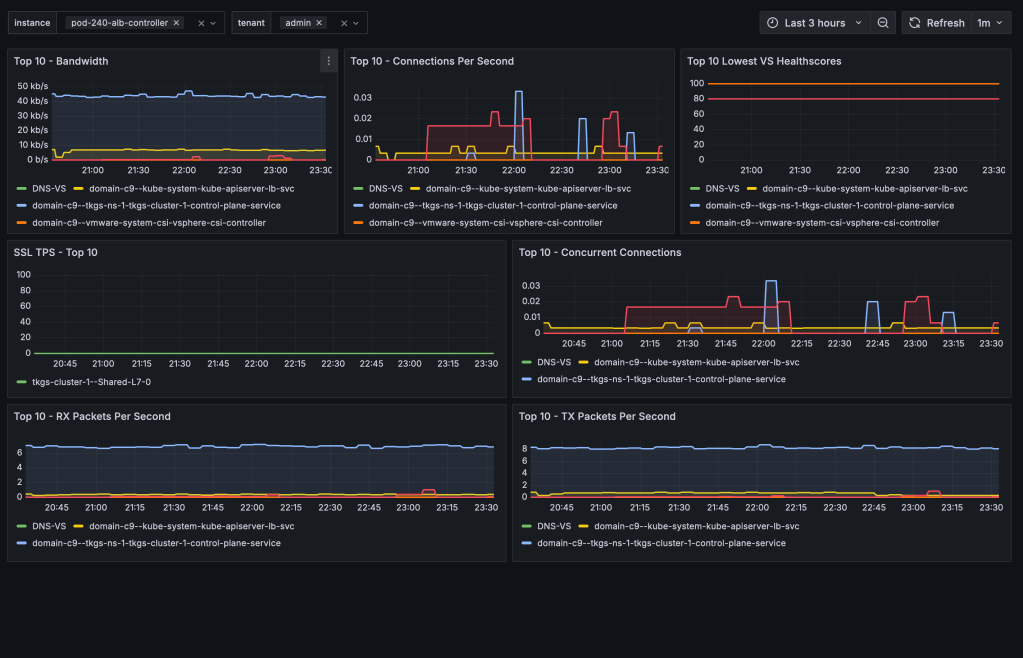
Avi Load Balancer offers a wealth of valuable metrics that can be accessed directly via the Avi Controller’s UI or API. However, there are various reasons why you might want to make these metrics available outside of its native platform. For instance, you might wish to avoid granting users or systems direct access to the…
-

TKG Service Clusters using the default Antrea CNI, can be easily configured for enhanced network visibility through flow visualization and monitoring. The ability to monitor network traffic within your Kubernetes clusters, as well as between your Kubernetes constructs and the outside world, is essential for understanding system behavior—and especially important when things aren’t working as…
-

Organizations aiming to leverage NSX for securing their TKG Service Clusters (Kubernetes clusters) can now achieve this with relative ease. In this guide, I’ll walk you through configuring the integration between a TKG Service Cluster and NSX—a required step for centrally managing security policies within TKG Service Clusters and between these clusters and external networks.…
-

Slow and steady. That’s how I would describe the pace and progress around making SDDC.Lab version 6 the new default and recommended version of the project. If you’re not familiar with the SDDC.Lab project, it’s a collection of Ansible Playbooks that perform fully automated deployments of nested VMware Software Defined Data Center environments called pods. Each…
-

As of NSX version 4.1.1, NSX Advanced Load Balancer version 22.1.4, and vSphere with Tanzu version 8.0 Update 2 we have the option to leverage the NSX Advanced Load Balancer as the load balancer provider for new vSphere with Tanzu backed by NSX networking deployments. This deployment option is a very welcome addition knowing that…